Federal Cloud Migration Without the 12-Month Security Audit Hangover
TL;DR / Executive Summary
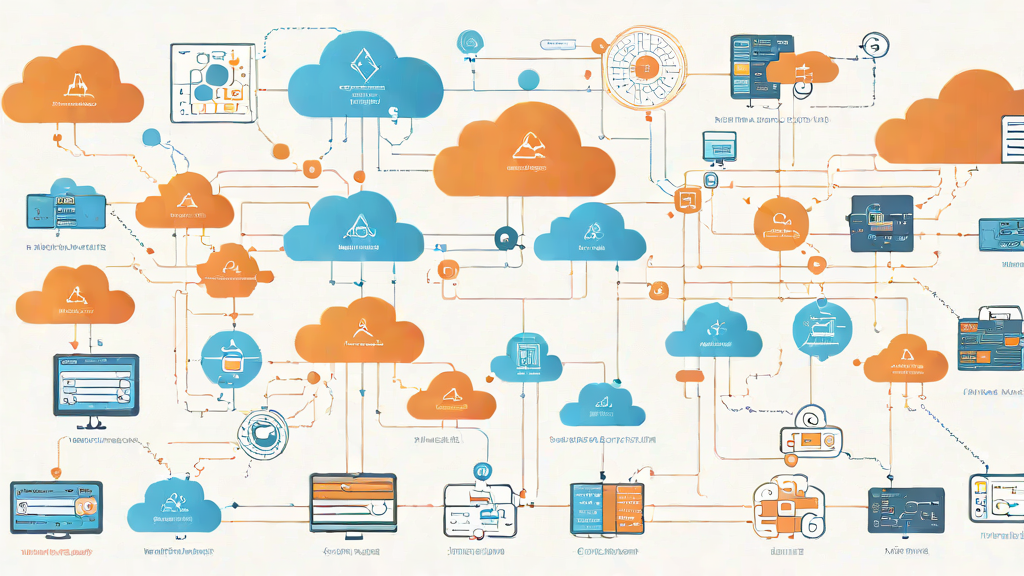
Federal agencies moving workloads to the cloud face a brutal reality: every migration triggers a new security assessment cycle. You’re not just moving applications — you’re re-proving compliance from scratch. The typical pattern? Spend 8-12 months migrating infrastructure, then discover your new cloud environment needs another 6-9 months of security documentation and assessment before you can actually deploy production workloads. Your timelines explode. Your teams burn out. Your agency’s modernization initiative becomes another cautionary tale.
The core problem isn’t cloud migration itself — it’s the compliance gap between “infrastructure deployed” and “Authority to Operate granted.” Most agencies treat these as sequential phases. They migrate first, document later. They build cloud-native architectures without embedding security controls from day one. They assume FedRAMP-authorized cloud platforms automatically inherit compliance. They don’t.
This article walks through the five migration-security disconnects crushing federal IT modernization — and shows how deterministic automation bridges the gap. You’ll learn how to assess applications using the 7R methodology, generate infrastructure-as-code with STIG hardening baked in, enforce CISA Secure by Design principles during migration, and maintain continuous compliance as you modernize. Not theory. Practical engineering that lets you migrate with security controls intact.
Introduction
You’ve been planning this cloud migration for 18 months. Business case approved. Budget secured. Cloud service provider selected. Migration team assembled. You’re ready to move the first batch of applications out of the data center and into AWS GovCloud.
Then your ISSO asks a simple question: “How are we maintaining our existing ATO during the migration?”
Silence.
Here’s what nobody tells you during the cloud sales pitch: moving to a FedRAMP-authorized cloud platform doesn’t automatically transfer your security controls. Your application still needs its own ATO. Your new cloud infrastructure — the VPCs, the IAM policies, the S3 buckets, the RDS databases — all need documented security controls mapped to NIST 800-53. The fact that AWS GovCloud holds a High FedRAMP authorization means you inherit some infrastructure controls. You still need to implement and document the rest.
Most agencies discover this gap mid-migration. They’ve already spun up cloud resources. Already started refactoring applications. Already committed to timelines based on infrastructure deployment, not security authorization. The result? Migration technically completes on schedule, but the new cloud environment sits empty for months while security teams scramble to backfill documentation.
Sound familiar?
The fundamental mistake is treating migration and security as separate workstreams. They’re not. Every migration decision — rehost vs. replatform, EC2 vs. containers, monolith vs. microservices — has direct compliance implications. Waiting until after migration to address these implications guarantees delay.
The Challenge
You’re Migrating Applications Without Migrating Their Security Posture
Federal agencies typically approach cloud migration as an infrastructure project. The migration team focuses on technical feasibility: Can we lift-and-shift this application to EC2? Should we refactor to containers? Do we need to re-architect for serverless?
These are the right technical questions. But they’re incomplete.
The missing question: What happens to our NIST 800-53 control implementations when we move this application to the cloud?
Take AC-2 (Account Management) as a concrete example. In your on-premises environment, you’ve documented how Active Directory enforces password complexity, account lockout, and role-based access. You’ve mapped these implementations to specific AC-2 control requirements. Your ATO package includes this documentation.
Now you’re migrating to AWS. Your application will use AWS IAM instead of Active Directory. Your password policies move to IAM password policy configuration. Your account lockout becomes IAM credential report monitoring. Your role-based access becomes IAM roles and policies.
Same control requirement. Completely different implementation.
Here’s the brutal part: your existing ATO documentation doesn’t cover the new implementation. Your migration team built the IAM policies. Your security team has no idea what’s in them. Your ISSO can’t verify AC-2 compliance in the new environment because the control implementation has fundamentally changed.
Multiply this across 421 NIST 800-53 controls. That’s the compliance gap.
Most agencies realize this too late. They migrate first, discover the gap during the first cloud security assessment, then spend 6-9 months rebuilding control documentation from scratch. They interview the migration team to reverse-engineer security decisions. They audit CloudTrail logs to understand what access patterns actually exist. They try to map AWS Config rules back to NIST controls without clear traceability.
This isn’t a documentation problem. It’s an architecture problem.
Your 7R Migration Decisions Happen in a Compliance Vacuum
The 7R framework — Rehost, Replatform, Refactor, Rearchitect, Rebuild, Replace, Retire — gives agencies a structured way to categorize migration approaches. Each application gets assessed and slotted into one of these strategies based on technical feasibility, cost, and business value.
What’s missing? Security control impact analysis.
A rehost migration (lift-and-shift) typically has the smallest compliance footprint. You’re moving the application as-is to cloud infrastructure. Most of your application-level controls remain unchanged. Your compliance burden focuses on documenting the infrastructure controls in the new cloud environment.
A rearchitect migration (microservices, serverless, containerization) has massive compliance implications. You’re fundamentally changing how the application implements authentication, authorization, logging, encryption, and network segmentation. Every architectural decision introduces new controls that need documentation.
But agencies make 7R decisions without this analysis. The migration team evaluates applications based on technical debt and modernization value. They recommend rearchitecting the monolith because it’s a technical improvement. They’re not wrong — it is a technical improvement. But nobody calculated the compliance cost.
Here’s a real scenario: you have a legacy Java monolith running on physical servers in your data center. It’s been through three ATO cycles. Your control documentation is mature. Your ISSO knows exactly how every control is implemented.
Your migration team recommends Rearchitect: break the monolith into microservices, containerize everything, deploy to Amazon EKS. From a modernization perspective, this makes perfect sense. You’ll gain scalability, resilience, and developer velocity.
From a compliance perspective, you just triggered a complete ATO rewrite.
Your authentication implementation moves from LDAP to OAuth2 with AWS Cognito. Your authorization logic moves from application code to API Gateway resource policies and Lambda execution roles. Your logging moves from log4j files to CloudWatch Logs with structured JSON. Your network segmentation moves from VLAN-based isolation to Kubernetes network policies and AWS security groups.
None of this is documented in your existing ATO package. You’ve essentially built a new application from a compliance perspective. And you won’t realize it until you’re 8 months into the migration, knee-deep in container orchestration, facing a 12-month delay to redo security documentation.
The core issue: 7R decisions should include compliance impact scoring. Rehost gets a low compliance burden score. Rearchitect gets a high score. Agencies need this data to make informed tradeoffs between modernization value and security authorization timelines.
They’re making these decisions blind.
You’re Generating Infrastructure-as-Code Without Security Hardening
Infrastructure-as-Code (IaC) is the foundation of repeatable cloud deployments. Terraform templates define your VPCs, subnets, security groups, IAM roles, S3 buckets, RDS instances. You version control these templates. You peer review changes. You apply them consistently across environments.
This is cloud engineering best practice. No argument.
But most agencies write IaC focused on functionality, not compliance. Their Terraform templates provision resources that work. They don’t provision resources that meet DISA STIG requirements.
Take S3 bucket encryption as a specific example. The STIG for AWS (V2R1) includes finding V-256949: “The AWS S3 bucket must have server-side encryption enabled.” Your Terraform template needs to include:
resource "aws_s3_bucket_server_side_encryption_configuration" "example" {
bucket = aws_s3_bucket.example.id
rule {
apply_server_side_encryption_by_default {
sse_algorithm = "AES256"
}
}
}
Most agency Terraform templates don’t include this. Why? Because the S3 bucket works fine without it. Encryption is a security requirement, not a functional requirement. Developers focused on getting infrastructure deployed don’t naturally prioritize STIG findings.
The result: you deploy cloud infrastructure that technically functions but fails security scans. Your ISSO runs SCAP compliance checks against your AWS environment and generates 200+ STIG findings. You spend the next 3 months remediating infrastructure you thought was already compliant.
This pattern repeats across every resource type. Security groups allow 0.0.0.0/0 ingress when they should restrict to specific CIDR blocks. IAM policies grant * permissions when they should follow least privilege. RDS instances don’t enforce encryption at rest. EC2 instances aren’t configured for CloudWatch detailed monitoring.
None of these are deliberate security failures. They’re gaps in the IaC generation process.
What agencies need: Terraform templates that include STIG hardening by default. Not as an afterthought. Not as a manual remediation step. Baked into the IaC from day one.
ICDEV™ (https://github.com/icdev-ai) addresses this directly through its multi-cloud infrastructure-as-code generation capability. You specify your target CSP — AWS GovCloud, Azure Government, GCP Assured, OCI Government, IBM IC4G, or air-gapped local deployment — and the system generates Terraform templates with DISA STIG hardening already applied.
One IaC generation engine for six cloud service providers. Every S3 bucket includes encryption configuration. Every security group follows least privilege. Every IAM role includes session duration limits. Every RDS instance enforces encryption at rest. The generated code isn’t just functional — it’s compliant.
Here’s the practical workflow:
This command assesses your project’s impact level (IL2 through IL6) and generates the appropriate hardening profile. The system then applies this profile to all infrastructure code generation. You’re not manually adding encryption blocks to every S3 bucket. The generator does it automatically based on your impact level requirements.
The compliance bridge for NIST control inheritance takes this further. When you deploy to a FedRAMP-authorized CSP, you inherit certain infrastructure controls from the cloud platform’s authorization. ICDEV™ automatically documents which controls you inherit vs. which controls you need to implement yourself. You’re not guessing. You’re not manually reading FedRAMP authorization packages to figure out the inheritance boundaries.
The system maps your infrastructure code to NIST 800-53 controls, flags inherited controls, and generates implementation documentation for the controls you own. Your IaC becomes the source of truth for security compliance, not a separate artifact you need to reconcile.
Your Pre-Merge Security Checks Don’t Catch Compliance Drift
Most federal development teams have adopted some form of CI/CD pipeline security scanning. Pull requests trigger SAST scans, dependency audits, secret detection. Developers get feedback before code merges. This catches obvious vulnerabilities.
But it doesn’t catch compliance drift.
Compliance drift happens when a code change is technically secure but violates a documented control implementation. Your SAST scan finds no vulnerabilities. Your dependency audit shows no CVEs. Your secret scanner finds no hardcoded credentials. The code looks clean.
Then your ISSO reviews it and realizes you just changed how user sessions are managed — and the new implementation doesn’t match your documented CM-6 configuration management control.
This is the gap between “secure code” and “compliant code.” They’re not the same thing.
Here’s a concrete scenario: your ATO documentation states that user sessions expire after 15 minutes of inactivity (AC-12, Session Termination). A developer submits a PR that changes the session timeout to 30 minutes to improve user experience. The code review focuses on implementation quality. The security scan focuses on vulnerabilities. Nobody catches that this violates your documented control.
The code merges. Deploys to production. Six months later during your annual assessment, your auditor discovers the discrepancy. Now you have three options: (1) roll back the code change, (2) update your ATO documentation and re-justify the 30-minute timeout to your authorizing official, or (3) accept a POAM and commit to remediating within 120 days.
All three options are painful. All three were avoidable.
The root cause: your PR security checks don’t have compliance awareness. They scan for vulnerabilities in isolation. They don’t know what control implementations exist in your current ATO package. They can’t detect when a code change introduces compliance drift.
What you need: diff-based compliance analysis that runs on every PR.
ICDEV™’s PR Intelligence capability solves this by integrating compliance control impact detection into your existing GitHub workflow. Every pull request triggers:
- Diff-based SAST — only scans changed code (keeps PR checks fast even in large codebases)
- Compliance control impact detection — flags code changes that affect documented control implementations
- Auto-POAM generation — creates a Plan of Action & Milestones entry for any new security findings
This command analyzes the current PR, compares the diff against your documented controls, and reports any compliance impacts. Your developers get feedback in the PR comment thread before the code merges. No more discovering compliance drift months later during an assessment.
The key difference: this isn’t just scanning for vulnerabilities. It’s scanning for compliance impacts. If a developer changes session timeout configuration, the system detects that this affects AC-12 (Session Termination) and flags it for ISSO review. If a developer modifies encryption key rotation logic, the system detects that this affects SC-12 (Cryptographic Key Establishment and Management) and blocks merge until the change is documented.
You’re enforcing compliance at the same point where you enforce code quality. Not as a separate process. Not as a post-deployment audit. At the PR level.
You’re Migrating Applications Without Validating Secure by Design Principles
CISA’s Secure by Design initiative published 35 requirements that shift security accountability to software manufacturers. The directive is clear: security can’t be an add-on. It must be built into the development process from the start.
But most federal agencies migrating to the cloud don’t assess whether their migration approach actually meets these requirements.
Take SBD-05: “Ensure all code is subjected to static application security testing (SAST).” Straightforward requirement. Easy to implement in a greenfield project — just add SAST to your CI/CD pipeline.
But what about a lift-and-shift migration of a 10-year-old Java monolith? You’re moving it to EC2 as-is. You’re not refactoring. You’re not rewriting. The application has never been subjected to SAST because it predates your modern CI/CD practices.
Does this violate SBD-05? Technically yes. Practically, you can’t retrofit SAST into a legacy codebase without addressing thousands of findings. Do you block the migration until you remediate every finding? Do you create a security exception with a 365-day remediation plan? Do you accept the risk and document it in your POAM?
These are judgment calls. But agencies can’t make informed judgments without assessment data.
Most migration teams don’t run Secure by Design assessments before migration decisions. They select the 7R strategy, build the migration plan, execute the migration — and only later discover they’re not meeting SBD requirements in the new environment.
ICDEV™’s SBD assessment tool addresses this by mapping all 35 Secure by Design requirements to the Cloudyrion 8-pillar framework. You can assess any project against SBD requirements, identify gaps, and generate remediation plans before you migrate.
This command runs a full SBD assessment with gate enforcement. If any requirement fails, the assessment blocks and reports which controls need remediation. You’re not discovering SBD gaps after migration. You’re validating compliance as part of your migration planning.
The security exception registry takes this further by enforcing max 365-day lifecycles on all exceptions. If you grant a temporary exception for SBD-05 (SAST requirement) because you’re migrating a legacy application, the system tracks the exception expiration date. After 365 days, the exception automatically expires and blocks deployment.
This prevents exception drift — where temporary exceptions become permanent because nobody tracks expiration. Your migration may start with SBD exceptions. But the system enforces a deadline for getting into full compliance.
How ICDEV™ Addresses These Challenges
Embedding Security Control Mapping into 7R Assessment
The reason agencies migrate applications without migrating their security posture is simple: they don’t have a structured way to assess compliance impact during migration planning.
ICDEV™’s legacy modernization and cloud migration capability includes 7R methodology assessment with compliance bridge analysis. For each application being evaluated, the system:
- Analyzes the current architecture and control implementations
- Maps existing NIST 800-53 controls to application components
- Simulates each 7R strategy (Rehost through Retire)
- Calculates compliance impact scores for each strategy
- Generates a migration recommendation with security tradeoffs
The output is a decision matrix that shows technical feasibility and compliance burden for each approach.
For a legacy monolith, you might see:
- Rehost (Lift-and-Shift): Low compliance impact, minimal control changes, fastest ATO update path
- Replatform (Managed Services): Medium compliance impact, some control implementations shift to cloud provider, moderate ATO update effort
- Rearchitect (Microservices): High compliance impact, most controls need reimplementation and documentation, significant ATO rewrite required
This data lets you make informed migration decisions. If your priority is speed, you choose Rehost despite the technical debt. If your priority is modernization and you have budget for a 9-month ATO update, you choose Rearchitect.
But you’re choosing with full visibility into compliance consequences. Not guessing.
The strangler fig pattern tracking capability supports incremental migration while maintaining compliance continuity. Instead of migrating the entire application in one high-risk cutover, you gradually replace components while keeping the legacy system operational. The tracking system maintains bidirectional control mapping — documenting how controls are implemented in both the legacy environment and the new cloud environment during the transition period.
Your ISSO can validate compliance at any point during the migration. Not just at the end when everything has been moved. At every increment.
Generating STIG-Hardened Infrastructure as Code from Day One
The gap between functional IaC and compliant IaC comes from manual hardening workflows. Developers write Terraform templates that deploy resources. Security teams audit those templates and generate lists of STIG findings. Developers remediate findings one by one.
This is slow. And it scales poorly.
ICDEV™ flips this model by generating STIG-hardened infrastructure code from the start. When you invoke the IaC generator, you specify:
- Target CSP: AWS GovCloud, Azure Government, GCP Assured, OCI Government, IBM IC4G, or air-gapped local
- Impact Level: IL2, IL4, IL5, or IL6 (drives hardening profile)
- Compliance Framework: NIST 800-53 Rev 5, DISA STIG, Platform One requirements
The system generates Terraform templates, Ansible playbooks, Kubernetes manifests, and Helm charts with all applicable hardening baked in.
For AWS GovCloud at IL4 (NIST 800-53 Moderate), this includes:
- S3 buckets with AES-256 encryption enabled by default
- Security groups restricted to specific CIDR blocks (no 0.0.0.0/0)
- IAM roles with session duration limits and MFA enforcement
- RDS instances with encryption at rest and automated backups
- VPC flow logs enabled and sent to CloudWatch Logs
- CloudTrail logging enabled across all regions
- AWS Config rules for continuous compliance monitoring
Every resource meets DISA STIG requirements before deployment. Your security team doesn’t need to audit and remediate after the fact. The IaC is compliant from the first terraform apply.
For Platform One Big Bang deployments, the system generates STIG-hardened Docker containers with Iron Bank metadata. These containers are ready for immediate deployment to DoD IL5 environments without additional hardening steps.
The compliance bridge for control inheritance automatically documents which NIST 800-53 controls you inherit from the FedRAMP-authorized CSP vs. which controls you need to implement yourself. Your generated IaC includes implementation code only for the controls you own. Inherited controls are flagged in the documentation but excluded from the code generation scope.
This prevents over-implementation — where agencies unnecessarily duplicate infrastructure controls that their CSP already provides.
The practical value: your infrastructure deployment and your ATO documentation are generated from the same source. When you update your Terraform templates, your control documentation automatically updates to reflect the change. You’re not maintaining two separate artifacts that drift over time.
Enforcing Secure by Design Principles with Automated Gating
CISA’s Secure by Design requirements aren’t optional recommendations. They’re increasingly becoming prerequisites for federal software procurement and deployment.
But enforcing 35 requirements across multiple applications, teams, and migration projects requires automation. Manual audits don’t scale.
ICDEV™’s SBD assessor maps all 35 requirements to the Cloudyrion 8-pillar framework:
- Authentication & Authorization (Pillars 1-2)
- Encryption & Data Protection (Pillar 3)
- Monitoring & Logging (Pillar 4)
- Vulnerability Management (Pillar 5)
- Secure Development (Pillar 6)
- Network Security (Pillar 7)
- Incident Response (Pillar 8)
Each SBD requirement maps to one or more pillars. The assessor scans your project, evaluates compliance for each requirement, and reports pass/fail status.
With --gate enforcement enabled, any failing requirement blocks deployment:
This shifts SBD validation left — into development and migration planning rather than post-deployment audit.
For migrations specifically, you run SBD assessment before selecting your 7R strategy. If you’re considering a Rehost migration of a legacy application that doesn’t meet SBD-05 (SAST requirement), the assessment flags this gap. You then have options:
- Grant a temporary exception with a 365-day remediation plan (tracked in the exception registry)
- Shift to a Refactor strategy that includes implementing SAST as part of the migration
- Retire the application instead of migrating if it can’t meet modern security baselines
The exception registry prevents SBD exceptions from becoming permanent:
Every exception includes:
- Requirement ID (e.g., SBD-05)
- Grant date
- Expiration date (max 365 days from grant date)
- Remediation plan
- Responsible party
After 365 days, expired exceptions automatically block deployment. Your team gets 30-day and 7-day warnings before expiration. You can’t ignore exceptions until they become compliance debt.
This enforcement model makes Secure by Design a hard requirement, not a soft guideline. Your migration can proceed with temporary exceptions if needed. But the system enforces a deadline for reaching full compliance.
Detecting Compliance Drift at the Pull Request Level
Most agencies discover compliance drift during annual assessments or post-incident reviews. By then, the drift has been in production for months. Rolling back isn’t practical. Updating documentation isn’t sufficient. You’re stuck with a POAM.
ICDEV™’s PR Intelligence shifts compliance validation to the pull request workflow — before code merges, before deployment, before production impact.
When a developer submits a PR, the system:
- Diffs the changes against the current codebase
- Runs targeted SAST on modified files only (keeps PR checks fast)
- Identifies affected NIST controls by mapping code changes to documented implementations
- Flags compliance impacts in the PR comment thread
- Auto-generates POAMs for any new security findings
The developer sees immediate feedback:
⚠️ Compliance Impact Detected
This PR modifies session timeout configuration:
- Current value: 15 minutes (AC-12: Session Termination)
- New value: 30 minutes
Impact: This change affects your documented AC-12 control implementation.
Action Required:
- Update ATO documentation to reflect the new timeout value
- Obtain ISSO approval before merging
- Or revert to 15 minutes to maintain current compliance
This prevents silent compliance drift. The developer knows their change has compliance implications. The ISSO gets visibility into the change before it deploys. The team can make an informed decision: approve the change and update documentation, or reject the change to maintain current compliance.
For security findings (CVEs, SAST vulnerabilities, secrets), the system auto-generates POAM entries:
🔴 Security Finding
SAST detected SQL injection vulnerability in user_auth.py:42
POAM-2025-001:
- Control: SI-10 (Information Input Validation)
- Severity: High
- Remediation Deadline: 2025-03-15 (90 days)
- Status: Open
Your POAM tracking is automated from the point of detection. No manual entry. No spreadsheet updates. The POAM is created when the vulnerability is discovered and tracked through remediation.
The diff-based analysis keeps PR checks fast even in large codebases. If your PR modifies 3 files out of a 50,000-file repository, the SAST scan only analyzes those 3 files. You’re not scanning the entire codebase on every PR.
This makes compliance validation practical for high-velocity development teams. Your PR checks run in seconds, not minutes. Developers get compliance feedback as fast as they get code review feedback.
Maintaining Continuous Compliance Through Multi-Layer Scanning
Cloud environments are dynamic. Infrastructure changes constantly. Dependencies update. New vulnerabilities get disclosed. Containers get rebuilt.
Your compliance posture isn’t static. It drifts unless you maintain continuous validation.
ICDEV™’s comprehensive security scanning runs four-layer validation across your entire cloud environment:
Layer 1: SAST (Static Application Security Testing)
Scans application code for security vulnerabilities using Bandit for Python, ESLint for JavaScript, and language-specific analyzers for other runtimes. Detects SQL injection, XSS, insecure deserialization, hardcoded secrets, and other OWASP Top 10 risks.
Layer 2: Dependency Vulnerability Auditing
Scans all dependencies against CVE databases. Flags vulnerable libraries and generates remediation recommendations. Tracks transitive dependencies (dependencies of dependencies) to catch deep vulnerabilities.
Layer 3: Secret Detection
Scans code, configuration files, and environment variables for accidentally committed credentials, API keys, private keys, and tokens. Prevents credential leakage before it reaches version control.
Layer 4: Container Image Scanning
Scans Docker images for OS-level vulnerabilities, insecure base images, and misconfigurations. Generates Iron Bank hardening manifests for Platform One Big Bang deployment.
These four layers run continuously — in PR checks, in CI/CD pipelines, and in scheduled environment scans. You’re not waiting for annual assessments to discover vulnerabilities. You’re detecting and remediating in near-real-time.
For DoD Platform One deployments, the container scanning layer generates Iron Bank metadata automatically. Your STIG-hardened containers include the documentation needed for Big Bang approval without manual hardening workflows.
The integration point: all scan results feed into your POAM tracking system. New findings auto-generate POAM entries with severity-based remediation deadlines. High-severity findings get 30-day deadlines. Medium severity gets 90 days. Low severity gets 120 days.
Your security team isn’t manually triaging scan results and updating POAMs. The system handles it automatically.
Practical Steps You Can Take This Week
You don’t need to overhaul your entire migration strategy to start addressing these challenges. Start small. Pick one high-impact change and implement it this week.
Step 1: Run a 7R Compliance Impact Assessment on One Application
Choose one application currently in your migration backlog. Don’t try to assess your entire portfolio. Just one app.
Document its current control implementations — specifically authentication, authorization, logging, and encryption. These four areas have the highest compliance drift risk during migration.
For each 7R strategy (Rehost, Replatform, Refactor, Rearchitect, Rebuild, Replace, Retire), write down:
– Which controls change implementation
– Which controls get inherited from the CSP
– Which controls need new documentation
You’ll quickly see the compliance burden for each approach. This data will inform your migration decision better than technical feasibility alone.
If you’re using ICDEV™, run the automated 7R assessment:
The system generates the compliance impact matrix automatically. Compare the automated results against your manual documentation to validate accuracy.
Step 2: Generate STIG-Hardened IaC for Your Next Cloud Deployment
Pick your next infrastructure deployment — a new VPC, a new application environment, a new set of S3 buckets. Instead of writing Terraform templates manually and hardening later, generate STIG-compliant IaC from the start.
Define your requirements:
– CSP: AWS GovCloud, Azure Government, etc.
– Impact Level: IL2, IL4, IL5, IL6
– Compliance Framework: NIST 800-53, DISA STIG
Then generate the IaC with hardening baked in. Deploy. Validate that the deployed resources meet STIG requirements without remediation.
Measure the time saved: how many hours did you avoid spending on post-deployment hardening? That’s your ROI metric.
Step 3: Add SBD Assessment to One Migration Project
Choose one migration project currently in planning or execution. Run a Secure by Design assessment against the current state and the target state.
For the current state:
For the target state (your planned migration architecture):
Compare the results. Are you improving SBD compliance through migration? Or introducing new gaps?
If you’re introducing gaps, decide now: grant exceptions with 365-day remediation plans, or adjust your migration approach to maintain compliance.
Don’t wait until post-migration audit to discover SBD violations.
Step 4: Enable PR Intelligence on One Repository
Pick one active repository with frequent pull requests. Add PR Intelligence to your GitHub workflow.
For every new PR, run:
Configure your CI/CD pipeline to post results as PR comments. Developers will start getting compliance feedback inline with code review.
Track how many compliance impacts you catch before merge. Every impact caught at PR level is a compliance drift issue you prevented in production.
After two weeks, measure:
– How many PRs triggered compliance warnings?
– How many were fixed before merge vs. approved with documentation?
– How much time did your ISSO save by not discovering drift during assessments?
Step 5: Run a Four-Layer Security Scan on Your Cloud Environment
Pick one cloud environment — dev, test, staging, or production. Run all four security scans:
# Plus secret detection and container scanning
Aggregate all findings. Categorize by severity. Auto-generate POAM entries for everything.
Now you have a baseline compliance posture for that environment. Schedule these scans to run weekly. Track how your finding count trends over time. Are you remediating faster than new findings appear? Or is your compliance debt growing?
This metric tells you whether your current security workflow is sustainable or heading toward crisis.
Conclusion
Federal cloud migration isn’t failing because agencies lack cloud expertise. It’s failing because they’re migrating infrastructure without migrating security controls.
The gap between “infrastructure deployed” and “authority to operate granted” is where modernization timelines explode. Agencies spend 8-12 months moving workloads to the cloud, then discover they need another 6-9 months to rebuild compliance documentation from scratch.
This pattern is avoidable.
By embedding security control mapping into 7R assessment, generating STIG-hardened IaC from day one, enforcing Secure by Design principles with automated gating, detecting compliance drift at the PR level, and maintaining continuous validation through multi-layer scanning, agencies can migrate with security controls intact.
Not as an afterthought. As a core engineering practice.
The shift from “migrate first, document later” to “migrate with continuous compliance” requires tooling. Manual processes don’t scale. Spreadsheet-based POAM tracking doesn’t work for high-velocity cloud environments.
Deterministic automation does.
ICDEV™ provides the engineering foundation for compliant cloud migration. Not theory. Production tooling that federal development teams use to ship secure applications without sacrificing velocity.
Your next migration doesn’t have to end with a 9-month ATO delay. It can deploy to production with security controls validated from day one.
Related Reading: The 5 Compliance and Security Challenges Crushing Federal Software Teams in 2026 — And How Deterministic Automation Fixes Them — Explore more on this topic in our article library.
Get Started
Ready to migrate to the cloud without the 12-month security audit hangover?
Explore ICDEV™ on GitHub: https://github.com/icdev-ai
Clone the repository. Run